What we do
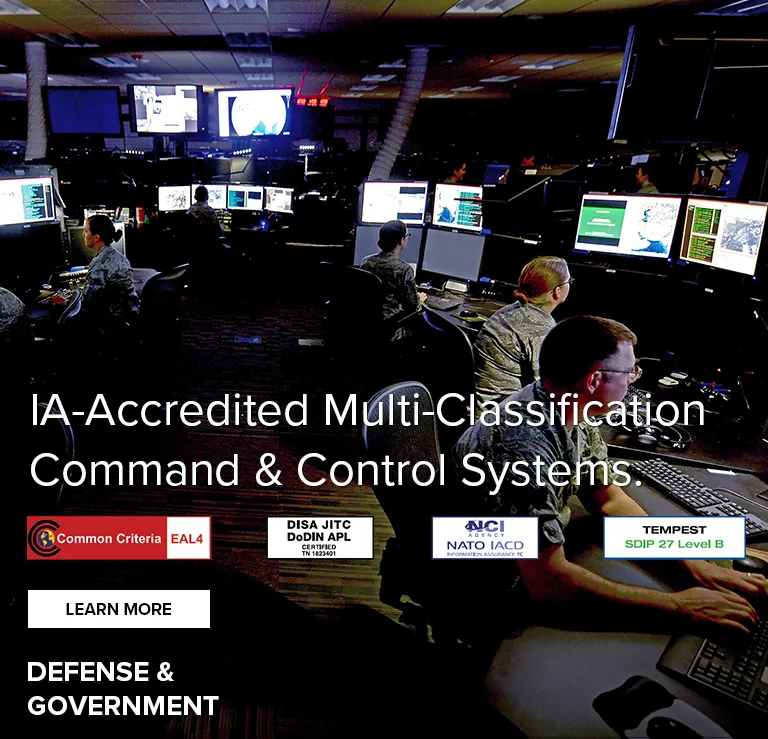
We help organizations securely manage video-rich workflows, leading to instant situational awareness, increased productivity and lower operational costs.
Our Advantage
We can deliver data from any source to any destination, instantaneously, providing authorized access to any network at any level of classification through a single, IA-accredited infrastructure. This streamlines workflows, increases responsiveness and reduces operational complexity, enabling collaboration and faster, better-informed decisions.
Thinklogical manufactures mid-to-large scale fiber-optic KVM matrix switches that are IA-accredited to manage multiple classifications of information through a single switch, simplifying authorized information access and improving operations center workflows.
Thinklogical products have achieved Common Criteria EAL4, NATO (NIAPC) Evaluation Scheme: GREEN status, DoDIN (JITC) APL, and TEMPEST SDIP 27 Level B certification for single chassis, multi-classification computer KVM and video distribution system (VDS) infrastructures.
With Thinklogical extenders and matrix switches, you can back rack computers and maintain Information Assurance (IA) certified isolation between multiple classified and non-classified networks through a single matrix switch. This reduces or eliminates the need to air-gap parallel networks at the desktop, increasing premise data security, simplifying AV and IT system management, and reducing overall infrastructure costs.
Our secure signal extension systems enable computers and VDI clients -- and their vulnerable USB ports, hard drives, and network interfaces -- to be removed from the workspace and back-racked in secure IT machine rooms. This increases premise cyber-security and reduces the chance of intentional hacking or accidental data loss or breach.
We dramatically reduce the amount of equipment and cabling required when compared to traditional AV and IT architectures, enabling resource sharing, lowering acquisition costs and simplifying ongoing management. This saves time and money while increasing flexibility to quickly reconfigure systems to meet changing mission requirements.





OUR PRODUCTS
Uncompressed Signal Management Solutions. Modular, Flexible, Resilient.
CONNECT WITH US
STATE-OF-THE-ART DEMO CENTERS
Learn hands-on best practices for achieving instant situational awareness. We’ve developed our fully-functional innovation centers to demonstrate real-world solutions for modern-day intelligence and security challenges. We’re able to show you firsthand how to build a flexible and secure command and control infrastructure that can enhance your operations and enable better-informed decision-making, while protecting the integrity of your network and data. Visit one of our command and control demonstration facilities in Vienna, Va., Milford, Conn., Tokyo, Japan and Canberra, Australia.BECOME AN EXPERT IN DEPLOYING A THINKLOGICAL VDS & KVM SYSTEM
Designed for sales engineers, design consultants, service and support personnel, Thinklogical Product and Technology training provides customers and partners with the tools they need to install and maintain a Thinklogical KVM system. Register for our online Tech 100 and Tech 151 level courses, available on-demand. Sign up for our Product and Technology 200 and 300 level classes, instructor-led, hands-on training courses offering in-depth education in advanced design, installation, and debugging of a Thinklogical KVM signal extension and switching system. EARN AVIXA CTS CREDITS Tech 100 – 6 RU Credits, Tech 200 – 4 RU Credits, Tech 300 – 8 RU Credits. No CTS RU Credits Available for Tech 151.COMPLIMENTARY DESIGN SERVICES
The Thinklogical Design Center (TLDC) is an invaluable resource available to our customers and partners. Led by an experienced team of AV, IT and KVM system experts, the TLDC works with customers and partners to provide conceptual system designs for requirements that range from the straightforward to the extremely innovative and complex. Typically, an initial TLDC consultation is a phone call lasting an hour or less. Initial system designs are usually completed within 24 hours. All TLDC services and consultations are complimentary.